- Out-of-Stock








DrayTek Vigor3900 Quad-WAN Load Balancing Router VPN Gateway, Internet 4 เส้น, NAT 120,000 Session, 950Mbps, QOS, VLAN, 4G LTE USB Modem
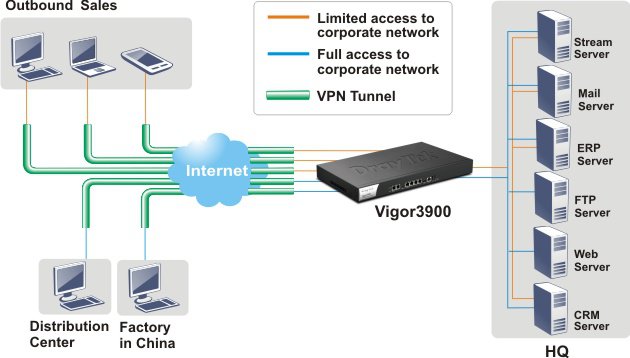
ต้องการเชื่อมเครือข่าย Network ไปยังสำนักงานด้วย VPN
DrayTek Vigor3900 Datasheet
DrayTek Vigor3900 User-Guide
DrayTek Vigor3900 Quick Guide
DrayTek Vigor3900 Product Specification |
|
|
Overview |
DrayTek Vigor3900 Quad-Wan Load-balance VPN Router, Internet 4 เส้น, NAT 120,000 Session, รองรับความเร็ว Internet 950Mbps VPN IPSec 500 Tunnels Throughput 900Mbps, 100 SSL VPN Throughput 400Mbps, Firewall, QOS, VLAN, รองรับ 4G LTE USB Modem |
Interface |
|
|
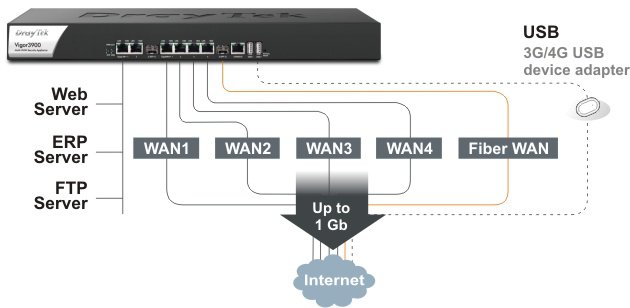
WAN Port |
4x GbE RJ-45 + 1x SFP |
|
LAN Port |
2x GbE RJ-45 + 1x SFP |
|
USB Port |
2 |
|
Console Port |
1x RJ-45 |
Performance |
|
|
NAT Throughput |
950 Mbps |
|
IPsec VPN Performance |
900 Mbps (ASE 256 bits) |
|
SSL VPN Performance |
400 Mbps (LAN-to-LAN) |
|
NAT Sessions |
120,000 |
|
Max. Concurrent VPN Tunnels |
500 |
|
Max. Concurrent OpenVPN + SSL VPN |
100 |
Internet Connection |
|
|
IPv4 |
PPPoE, DHCP, Static IP, PPTP |
|
IPv6 |
Link Local, Static, PPP, DHCP IA NA, DHCP IA PD |
|
Multi-VLAN |
|
|
3G/4G/LTE WAN with USB modem |
|
|
Outbound Load Balancing |
IP-based, Session-based |
|
Inbound Load Balancing |
|
|
Failover |
|
|
Connection Detection |
ARP, Ping, HTTP |
|
Dynamic DNS |
|
|
DrayDDNS |
|
LAN Management |
|
|
802.1q VLAN |
|
|
Max. Number of VLAN |
50 |
|
DHCP Server |
Multiple IP Subnet, Custom DHCP Options, Bind-IP-to-MAC |
|
PPPoE Server |
|
|
Port Mirroring |
|
|
Local DNS Server |
|
|
Conditional DNS Forwarding |
|
|
Web Portal |
|
|
Web Portal Authentication |
Local User Profile, Guest Profile, RADIUS, LDAP, SMS PIN |
Networking |
|
|
Static Routing |
IPv4 Static Routing, IPv6 Static Routing, Inter-VLAN Routing |
|
Dynamic Routing |
RIPv2, OSPFv2, BGP |
|
Policy-based Routing |
Protocol, IP Address, Port, Domain, Country |
|
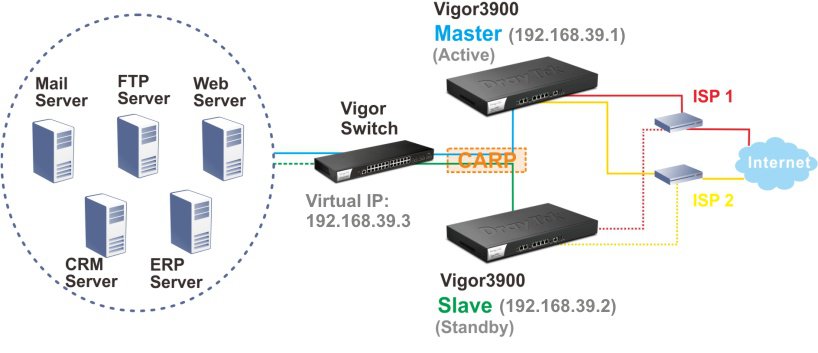
High Availability |
Active-Standby, Hot-Standby |
|
DNS Security (DNSSEC) |
|
|
GVRP |
|
|
Proxy |
IGMP, LAN ARP, WAN ARP |
|
SMB File Sharing |
(Requires external storage) |
VPN |
|
|
LAN-to-LAN |
|
|
Remote Dial-In (Teleworker-to-LAN) |
|
|
Protocols |
PPTP, L2TP, IPsec, L2TP over IPsec, SSL, GRE, IKEv2, IKEv2-EAP, IPsec XAuth, OpenVPN |
|
User Authentication |
Local, RADIUS, LDAP, mOTP |
|
IKE Authentication |
Pre-Shared Key, X.509 |
|
IPsec Authentication |
SHA-1, SHA-2/256, MD5 |
|
VPN Redundancy |
Load Balancing, Failover |
|
NAT-Traversal (NAT-T) |
|
Firewall & Content Filtering |
|
|
NAT |
Port Redirection, DMZ Host, UPnP |
|
ALG (Application Layer Gateway) |
SIP, FTP, H.323 |
|
VPN Pass-Through |
PPTP, L2TP, IPsec |
|
IP-based Firewall Policy |
|
|
Content Filtering |
Application, URL Keyword, File Extension, Web Category*, QQ Filter (*: subscription required) |
|
DoS Attack Defense |
|
Bandwidth Management |
|
|
IP-based Bandwidth Limit |
|
|
IP-based Session Limit |
|
|
QoS (Quality of Service) |
TOS, DSCP, 802.1p, IP Address, Service Type |
|
Hardware QoS |
|
|
VoIP Prioritization |
|
Management |
|
|
Local Service |
HTTP, HTTPS, Telnet, SSH, FTP, SAMBA, TR-069 |
|
Config File Export & Import |
|
|
Firmware Upgrade |
TFTP, HTTP, TR-069 |
|
2-Level Administration Privilege |
|
|
Access Control |
Access List, Brute Force Protection (Fail to Ban), Access Barrier |
|
Syslog |
|
|
Notification Alert |
SMS, E-mail |
|
SNMP |
v2, v2c, v3 |
|
Managed by VigorACS |
|
|
Central AP Management |
50 VigorAP |
|
Central Switch Management |
20 VigorSwitch |
|
Central VPN Management |
16 VPN |
Physical |
|
|
Rack Mountable |
Mouting Kit Included |
|
Dimension |
443 mm x 285 mm x 45 mm |
|
Weight |
2.86 kg |
|
Max. Power Consumption |
20 watts |
|
Operating Temperature |
0 to 45°C |
|
Storage Temperature |
-10 to 70°C |
|
Operating Humidity (non-condensing) |
10 to 90% |
|
รับประกัน |
2 ปี |
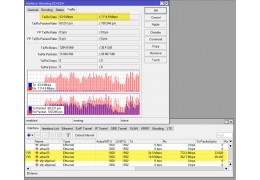
Multi-WAN Redundancy/ Load-balancing
High Availability
Mobile-OTP
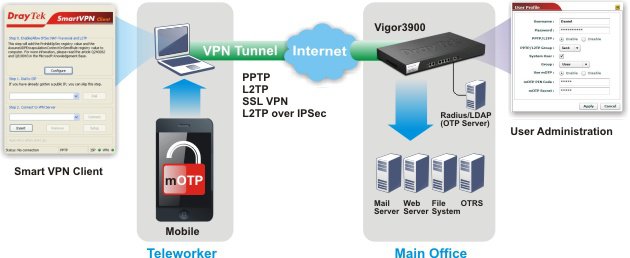
User Management
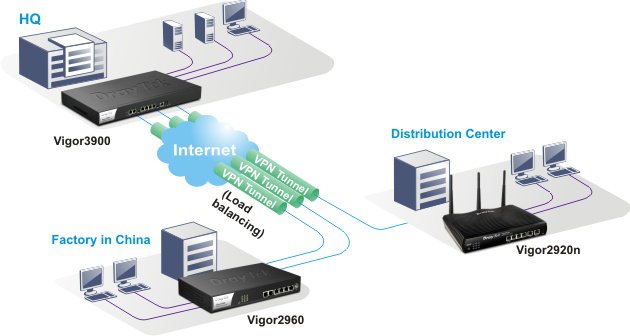
VPN Trunking
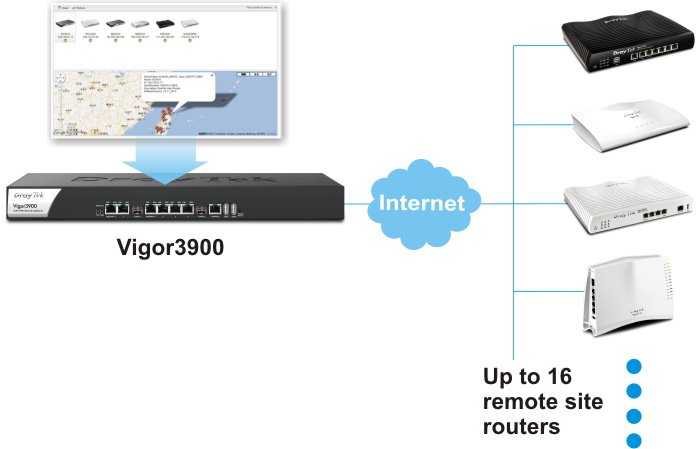
The CVM (Central VPN Management) of Vigor3900
Your review appreciation cannot be sent
Report comment
Report sent
Your report cannot be sent
Write your review
Review sent
Your review cannot be sent
แบรนด์: DrayTek
แบรนด์: DrayTek
แบรนด์: DrayTek
แบรนด์: DrayTek
 Review Draytek Vigor3910 Loadbalance Firewall รองรับ Internet สูงสุด 9.4Gbps
Review Draytek Vigor3910 Loadbalance Firewall รองรับ Internet สูงสุด 9.4Gbps
 ต้องการเชื่อมเครือข่าย Network ระหว่างสำนักงานด้วย VPN
ต้องการเชื่อมเครือข่าย Network ระหว่างสำนักงานด้วย VPN
 ต้องการทำ Loadbalance โดย Internet รวมแล้วมากกว่า 1Gbps
ต้องการทำ Loadbalance โดย Internet รวมแล้วมากกว่า 1Gbps
 Review Draytek รองรับ Wireguard VPN
Review Draytek รองรับ Wireguard VPN
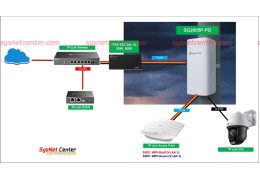 Review SG2005P-PD TP-LINK Omada POE Switch-POE IN/Out ติดตั้งภายนอกอาคาร
Review SG2005P-PD TP-LINK Omada POE Switch-POE IN/Out ติดตั้งภายนอกอาคาร

DrayTek Vigor3900 Quad-WAN Load Balancing Router VPN Gateway, Internet 4 เส้น, NAT 120,000 Session, 950Mbps, QOS, VLAN, 4G LTE USB Modem
check_circle
check_circle